Ronin’s $612M hack exposes these vulnerabilities of cross-chain bridges

For quite some time now, multi-chain or cross-chain technology has become a holy grail in the cryptocurrency development space. People want to transact with other blockchains by leveraging bridges to different ecosystems. For example, Ethereum co-founder and developer Vitalik Buterin tweeted a link to a Reddit post on 8 January, 2022.
He discussed his belief in a multi-chain future but expressed doubt concerning cross-chain ecosystems. In his argument, Buterin cited the “fundamental security limits of bridges” as the key reason for his disapproval of a cross-chain environment.
Although, he didn’t expect hiccups to arise any time soon. But note this – as the volume of cryptocurrency held in bridges grew, the incentive to attack them too.
Since then, hackers have compromised more than $1B despite such warnings.
Look away, Vitalik
Ronin Network, an Ethereum-based sidechain created by Axie Infinity developer Sky Mavis is trending for the wrong reason. Hackers stole nearly $600 million worth of Ethereum & USDC tokens from the Ronin Bridge that connected different blockchains.
According to a blog post published by the Ronin Network’s official Substack, the exploit affected Ronin Network validator nodes for Sky Mavis, the publishers of the popular Axie Infinity game, and the Axie DAO.
There has been a security breach on the Ronin Network.https://t.co/ktAp9w5qpP
— Ronin (@Ronin_Network) March 29, 2022
According to an official statement on Tuesday, the attacker “used hacked private keys to forge fake withdrawals” from the Ronin bridge contract in two transactions. Per the blog post, the Ronin sidechain consisted of nine validator nodes.
Five out of the nine validator signatures are required to process a deposit or withdrawal. Indeed, done to prevent hacks of this nature. (For context, Ethereum has around 300,000 validators, while Solana has closer to 1,000)
However, the blog post added:
“The attacker found a backdoor through our gas-free RPC node. They abused to get the signature for the Axie DAO validator.”
The Ronin bridge and Katana Dex got halted after suffering an exploit for 173,600 Ethereum (ETH) and 25.5 million USD Coin (USDC). At press time, it would be worth a combined $612 million.
We are working with law enforcement officials, forensic cryptographers, and our investors to make sure that all funds are recovered or reimbursed. All of the AXS, RON, and SLP on Ronin are safe right now.
— Ronin (@Ronin_Network) March 29, 2022
Just a headstart?
Now, here are some interesting insights into this heist. The said exploit took place on 23 March, only discovered a week later, when one user failed to withdraw 5,000 ETH.
Around 6,250 ether, or $21 million moved out of the attacker’s wallet address, including several ETH transferred to FTX Exchange, according to Etherscan.
Imagine stealing 600 million 6 days ago and depositing money on @FTX_Officialhttps://t.co/nYWYC1jJ1J pic.twitter.com/YGzr7uyk5Q
— Igor Igamberdiev (@FrankResearcher) March 29, 2022
Ahead of the exploit, the same wallet interacted with Binance, and other wallets connected to the hacker have since made deposits to FTX and Crypto.com. As per Wu Blockchain, the latest exodus took place as follows:
At 5:11:46 PM UTC on March 29, a total of 3750 ETH was transferred from three Ronin Bridge hacker address wallets into Huobi. The Ronin Bridge hack rarely intersects with many centralized exchange addresses. Previously transferred to FTX. https://t.co/T8OY9VKWeP
— Wu Blockchain (@WuBlockchain) March 30, 2022
Next steps
The Ronin team said it had increased the minimum number of validator signatures required for a deposit or withdrawal to eight in response to the incident. Different platforms had showcased support for the affected protocol post suffering this massacre. For instance, Binance’s CEO tweeted:
Our team is in touch with AxieInfinity team providing assistance in tracking this issue. https://t.co/pNU4wwrCAq
— CZ ? Binance (@cz_binance) March 29, 2022
Major damage: The price of RON, a token used on the Ronin blockchain, dropped about 22% after the hack. AXS, a token used in Axie Infinity, fell around 10.5% simultaneously. As per Bloomberg’s data, this hack stood at number two in terms of crypto hacks (valuation).
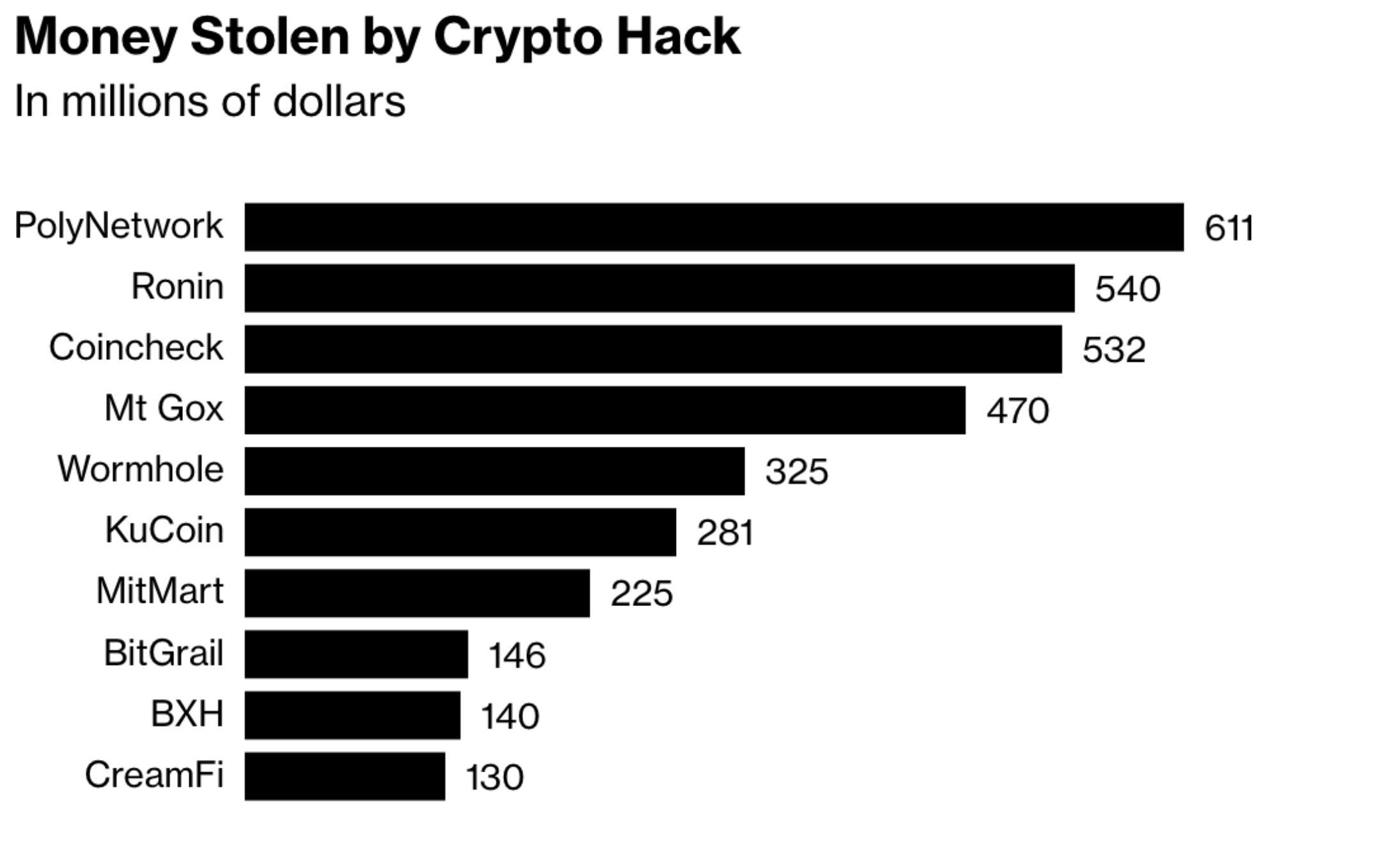
Source: Bloomberg
At the time of publication, most of the hacked funds are still sitting inside the attacker’s wallet.