Report: Hackers employ low-tech malwares to target individuals & steal millions

If it were measured as a country, then cyber-crime — which is predicted to inflict damages totaling $6 trillion globally in 2021 — would be the world’s third-largest economy after the U.S. and China.
Well, that’s quite an impressive yet unfortunate statistic. Now, different news had circulated in the past describing the highly sophisticated hacks thereby witnessing heavy losses. Fast forward now, “low-skilled cyber-criminals” were using malware to swipe funds from crypto HODLers.
Prey on the weak
A new malware report from blockchain analysis firm Chainalysis highlighted the same. Most tend to focus on high-profile ransomware attacks against big corporations and government agencies. However, here’s another angle. Cyber-criminals incorporated less sophisticated types of malware to steal millions in cryptocurrency from individual holders.
The usage of malware to steal or extort cryptocurrency is nothing new. In fact, less sophisticated hackers could take a cheaper “spray-and-pray” approach. Thereby, spamming millions of potential victims.
Malware refers to malicious software that carries out harmful activity on a victim’s device, usually without their knowledge. Malware-powered crime can be as simple as stealing information or money from victims, but can also be much more complex and grand in scale.
It ranges from information-stealing to denial-of-service (DDoS) attacks or ad fraud on a grand scale. Here’s the family tree:
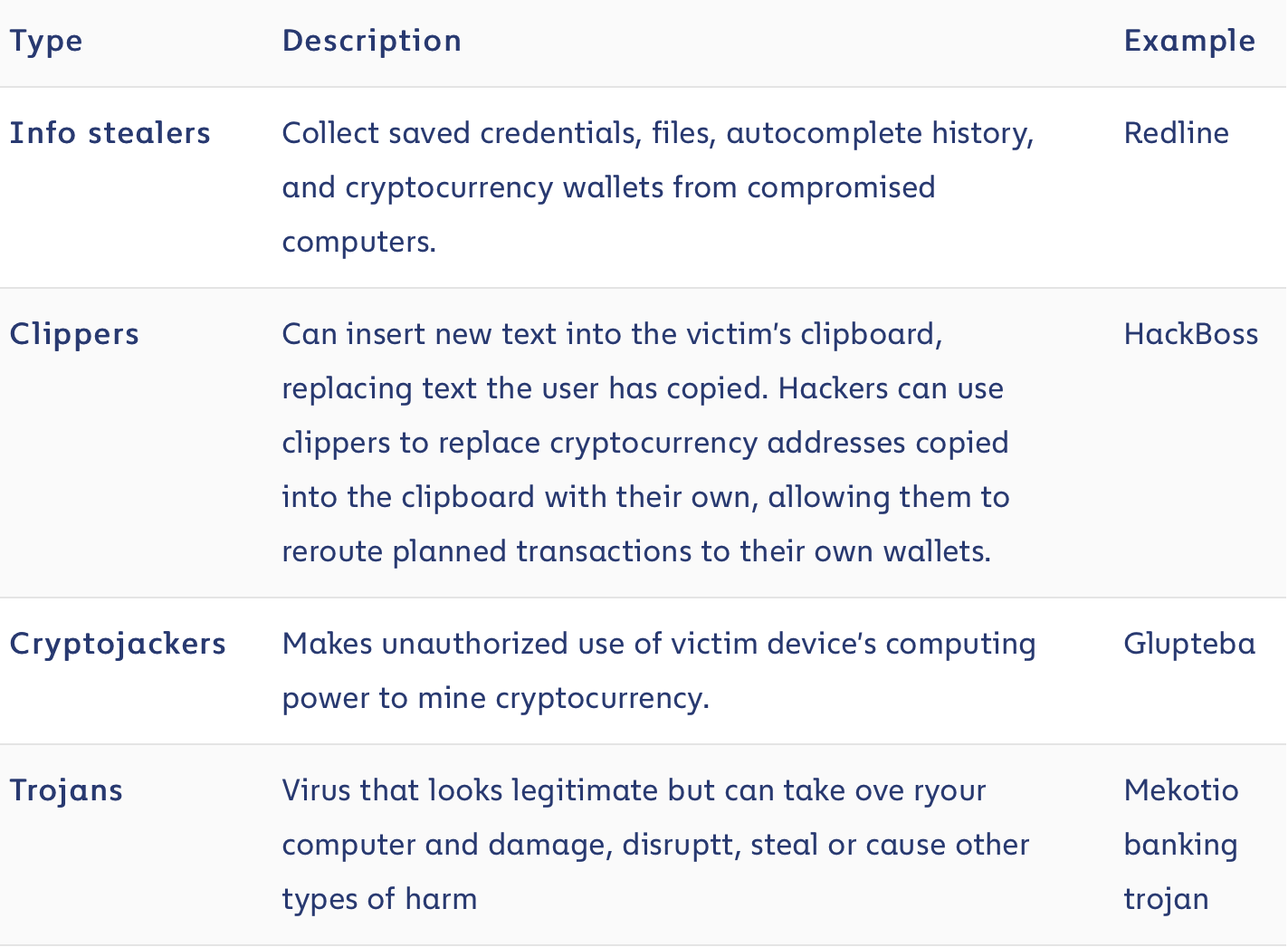
Source: Chainalysis
Many of the malware families described above were available to purchase for relatively little money on cyber-criminal forums.
Speaking numbers
Cryptojacking topped the list of values received via malware at 73%. Trojans came second at 19%, ‘Others’ totaled 5% while information stealers and clippers represented a mere 1% each. The pie-chart below highlighted the same.
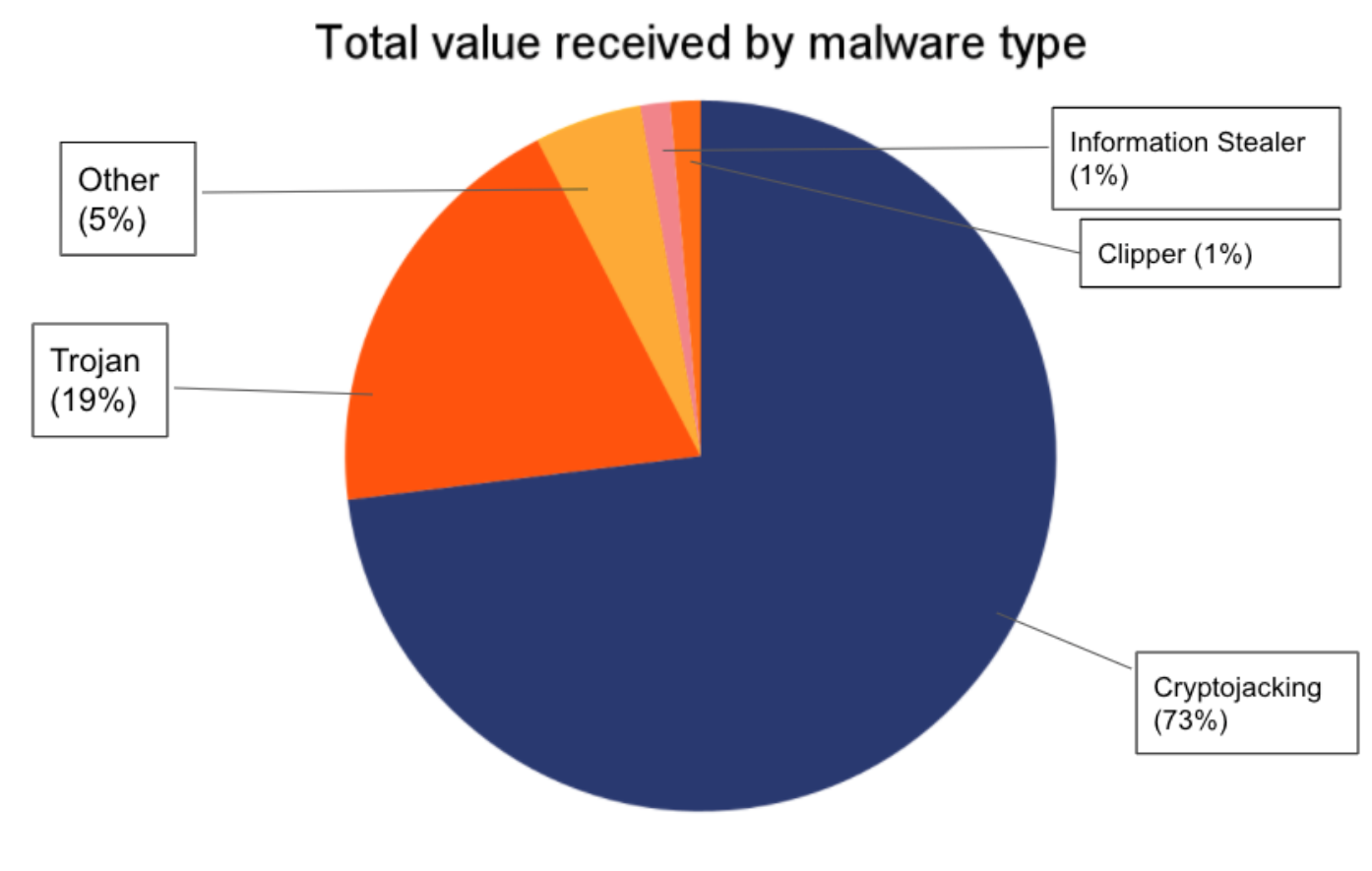
Source: Chainalysis
The aforementioned numbers were ‘likely only scratching the surface for cryptojacking.’ Although, such cases were witnessed on a massive scale. Consider this. In 2020, Cisco’s cloud security division reported that crypto-jacking malware affected 69% of its clients. This translates to an incredible amount of stolen computer power.
Getting slimmer
This was actually the case here. According to Chainalysis, malware addresses sent the “majority of funds on to addresses at centralized exchanges. However, this wasn’t the case (mostly).
“Exchanges only received 54% of funds sent from malware addresses in 2021, down from 75% in 2020. DeFi protocols make up much of the difference at 20% in 2021, after having received a negligible share of malware funds in 2020.”
Overall, industries do tend to focus more on attacks against large organizations. But over the last few years, there has been a shift. Hackers used malware to steal smaller amounts of cryptocurrency from individual users.
In fact, 43% of cyber attacks target small businesses in 2021 according to a report by the Purplesec.